SONAR — multivariate anomaly detection
Microsoft MTAD-GAT multivariate time-series anomaly detection on Wazuh alerts. Scenario-driven YAML configuration, offline debug mode, and direct RADAR data shipping in Wazuh.
IDPS-ESCAPE turns detection into action. It combines signature-based engines (Wazuh, Suricata) with machine learning anomaly detection to catch both known and emerging threats — then automatically fires risk-scaled responses, from alert emails to host isolation, enriched with live cyber threat intelligence. Incident cases are created automatically, closing the loop from detection to remediation. Built for SMEs, SOC teams, and CERT/CSIRT entities under the CyFORT project.
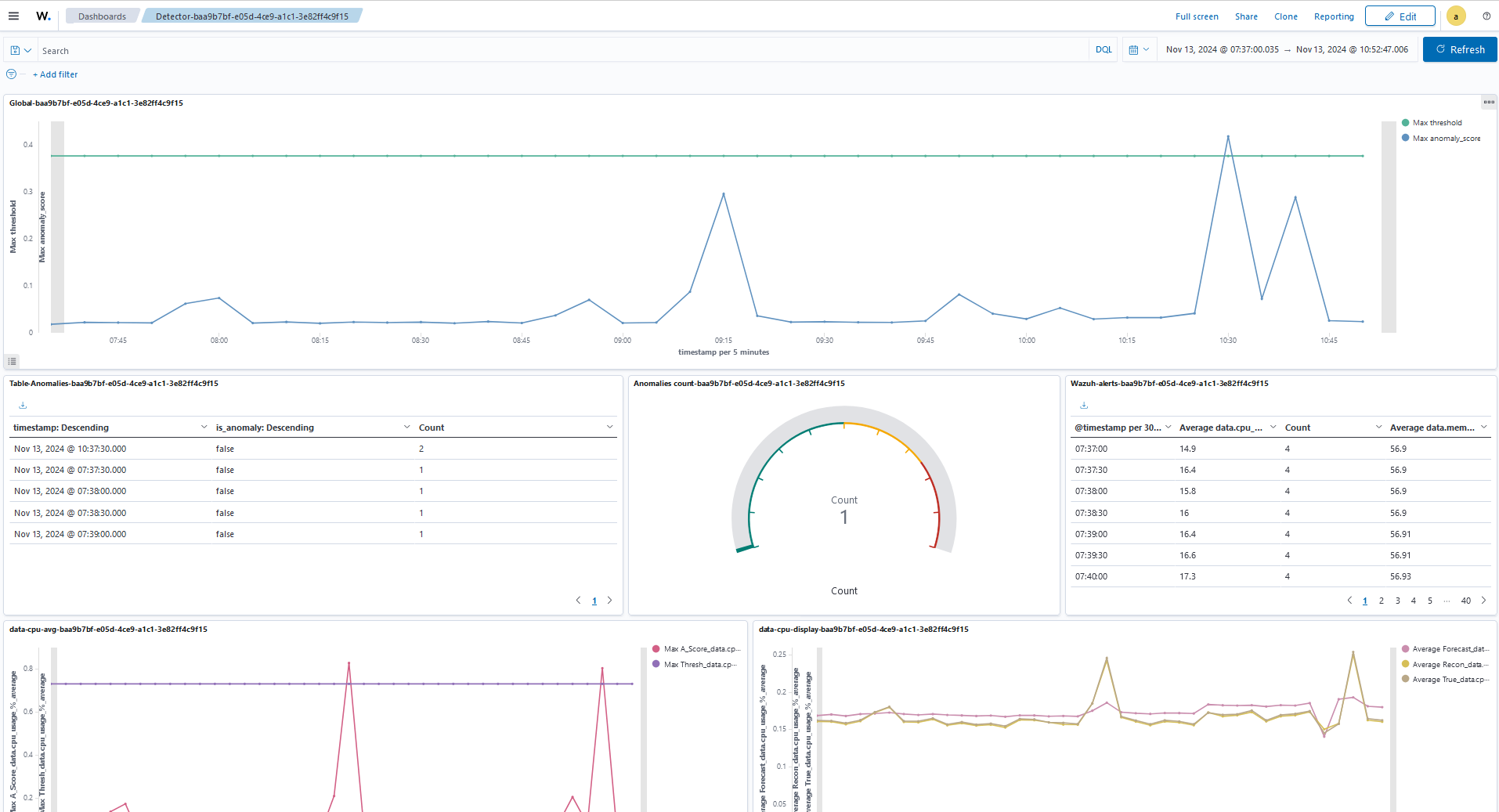
Microsoft MTAD-GAT multivariate time-series anomaly detection on Wazuh alerts. Scenario-driven YAML configuration, offline debug mode, and direct RADAR data shipping in Wazuh.
RRCF-based behavioral and signature detection with Ansible Infrastructure-as-Code deployment. Tiered active responses scale automatically to computed risk level.
Three-layer defense in depth: Wazuh/Suricata signature rules catch known patterns, RADAR (RRCF) detects behavioral anomalies, and SONAR (MTAD-GAT) identifies multivariate ML anomalies.
SATRAP-DL's DECIPHER subsystem queries MISP IOC feeds for blacklisted IPs, malicious domains, and hash indicators. The resulting CTI score T is fused into the normalized risk score R.
Incident cases are created automatically by DECIPHER in Flowintel when risk thresholds are crossed. Alert emails include the case URL, risk score breakdown, and full IOC context.
Zero-touch deployment of Wazuh manager and agents, OpenSearch AD detectors, monitors, webhooks, and active response scripts via reproducible Ansible playbooks.
Browser-based Flask interface for the full RADAR operational lifecycle: configure connectors, manage Wazuh inventory, tune risk weights and tier thresholds per scenario, deploy via Ansible, and monitor infrastructure health — all without touching configuration files directly.
Wazuh agents and Suricata sensors collect logs, network events, and endpoint telemetry, feeding the OpenSearch indexer in real time.
SONAR (MTAD-GAT multivariate ML) and RADAR (RRCF behavioral) detect anomalies. Wazuh rules simultaneously match known signature attack patterns.
The RADAR risk engine fuses anomaly intensity A, signature risk S, and DECIPHER CTI score T into a weighted R = wₐ·A + wₛ·S + wₜ·T, assigning a Low, Medium, or High response tier.
Active responses fire automatically: email alerts, Flowintel incident case creation, and strong actions (IP block, host isolation, credential disable) scaled to the risk tier.
DECIPHER queries MISP IOC feeds to keep threat intelligence current. Flowintel accumulates case history and SONAR models are retrained with fresh alert evidence.